[May-2016-Valid]Official 70-640 Exam PDF and VCE Dumps Free Offered[NQ21-NQ30]
2016 May Microsoft New Released: 70-640: Windows Server 2008 Active Directory, Configuring Exam Questions Updated Today in Braindump2go.com Online IT Certifications Study Website!
NEW QUESTIONS 21 – NEW QUESTIONS 30
QUESTION 21
You need to remove the Active Directory Domain Services role from a domain controller named DC1.
What should you do?
A. Run the netdom remove DC1 command.
B. Run the Dcpromo utility.
Remove the Active Directory Domain Services role.
C. Run the nltest /remove_server: DC1 command.
D. Reset the Domain Controller computer account by using the Active Directory Users and
Computers utility.
Answer: B
Explanation:
http://technet.microsoft.com/en-us/library/cc771844%28v=ws.10%29.aspx
QUESTION 22
Your company has an Active Directory forest.
The company has branch offices in three locations.
Each location has an organizational unit.
You need to ensure that the branch office administrators are able to create and apply GPOs only to their respective organizational units.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Run the Delegation of Control wizard and delegate the right to link GPOs for their branch
organizational units to the branch office administrators.
B. Add the user accounts of the branch office administrators to the Group Policy Creator Owners
Group.
C. Modify the Managed By tab in each organizational unit to add the branch office administrators
to their respective organizational units.
D. Run the Delegation of Control wizard and delegate the right to link GPOs for the domain to the
branch office administrators.
Answer: AB
Explanation:
http://technet.microsoft.com/en-us/library/cc732524.aspx
QUESTION 23
One of the remote branch offices is running a Windows Server 2008 read only domain controller (RODC).
For security reasons you don’t want some critical credentials like (passwords, encryption keys) to be stored on RODC.
What should you do so that these credentials are not replicated to any RODC’s in the forest? (Select 2)
A. Configure RODC filtered attribute set on the server
B. Configure RODC filtered set on the server that holds Schema Operations Master role.
C. Delegate local administrative permissions for an RODC to any domain user without granting
that user any user rights for the domain
D. Configure forest functional level server for Windows server 2008 to configure filtered attribute
set.
E. None of the above
Answer: BD
Explanation:
http://technet.microsoft.com/en-us/library/cc753223.aspx
Adding attributes to the RODC filtered attribute set
The RODC filtered attribute set is a dynamic set of attributes that is not replicated to any RODCs in the forest. You can configure the RODC filtered attribute set on a schema master that runs Windows Server 2008. When the attributes are prevented from replicating to RODCs, that data cannot be exposed unnecessarily if an RODC is stolen or compromised.
A malicious user who compromises an RODC can attempt to configure it in such a way that it tries to replicate attributes that are defined in the RODC filtered attribute set. If the RODC tries to replicate those attributes from a domain controller that is running Windows Server 2008, the replication request is denied. However, if the RODC tries to replicate those attributes from a domain controller that is running Windows Server 2003, the replication request could succeed.
Therefore, as a security precaution, ensure that forest functional level is Windows Server 2008 if you plan to configure the RODC filtered attribute set. When the forest functional level is Windows Server 2008, an RODC that is compromised cannot be exploited in this manner because domain controllers that are running Windows Server 2003 are not allowed in the forest.
QUESTION 24
Company has a server with Active Directory Rights Management Services (AD RMS) server installed.
Users have computers with Windows Vista installed on them with an Active Directory domain installed at Windows Server 2003 functional level.
As an administrator at Company, you discover that the users are unable to benefit from AD RMS to protect their documents.
You need to configure AD RMS to enable users to use it and protect their documents.
What should you do to achieve this functionality?
A. Configure an email account in Active Directory Domain Services (AD DS) for each user.
B. Add and configure ADRMSADMIN account in local administrators group on the user
computers
C. Add and configure the ADRMSSRVC account in AD RMS server’s local administrator group
D. Reinstall the Active Directory domain on user computers
E. All of the above
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/cc753531%28v=ws.10%29.aspx
AD RMS Step-by-Step Guide
For each user account and group that you configure with AD RMS, you need to add an e- mail address and then assign the users to groups.
QUESTION 25
Company has an active directory forest on a single domain.
Company needs a distributed application that employs a custom application.
The application is directory partition software named PARDAT.
You need to implement this application for data replication.
Which two tools should you use to achieve this task? (Choose two answers. Each answer is a part of a complete solution)
A. Dnscmd.
B. Ntdsutil.
C. Ipconfig
D. Dnsutil
E. All of the above
Answer: AB
Explanation:
http://support.microsoft.com/kb/884116
How to create and apply a custom application directory partition on an Active Directory integrated DNS zone in Windows Server 2003
You can create a custom Active Directory partition by using the DnsCmd command. If the new naming context that you created does not appear in the Repadmin output, you can verify the state of this naming context by using the Ntdsutil command.
QUESTION 26
Company has an Active Directory forest with six domains.
The company has 5 sites.
The company requires a new distributed application that uses a custom application directory partition named ResData for data replication.
The application is installed on one member server in five sites.
You need to configure the five member servers to receive the ResData application directory partition for data replication.
What should you do?
A. Run the Dcpromo utility on the five member servers.
B. Run the Regsvr32 command on the five member servers
C. Run the Webadmin command on the five member servers
D. Run the RacAgent utility on the five member servers
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/cc732887%28v=ws.10%29.aspx
Dcpromo Syntax dcpromo [/answer[:<filename>] | /unattend[:<filename>] | /unattend | /adv] /uninstallBinaries [/CreateDCAccount | /UseExistingAccount:Attach] /? /?[:{Promotion | CreateDCAccount | UseExistingAccount |Demotion}]dcpromo Promotion operation parameters:
ApplicationPartitionsToReplicate:””
Specifies the application directory partitions that dcpromo will replicate.
Use the following format: “partition1” “partition2” “partitionN”
Use * to replicate all application directory partitions.
QUESTION 27
As an administrator at Company, you have installed an Active Directory forest that has a single domain.
You have installed an Active Directory Federation services (AD FS) on the domain member server.
What should you do to configure AD FS to make sure that AD FS token contains information from the active directory domain?
A. Add a new account store and configure it.
B. Add a new resource partner and configure it
C. Add a new resource store and configure it
D. Add a new administrator account on AD FS and configure it
E. None of the above
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/cc772309%28v=ws.10%29.aspx
Step 3: Installing and Configuring AD FS
Now that you have configured the computers that will be used as federation servers, you are ready to install Active Directory Federation Services (AD FS) components on each of the computers. This section includes the following procedures:
Install the Federation Service on ADFS-RESOURCE and ADFS-ACCOUNT
Configure ADFS-ACCOUNT to work with AD RMS
Configure ADFS-RESOURCE to Work with AD RMS
QUESTION 28
Company runs Window Server 2008 on all of its servers.
It has a single Active Directory domain and it uses Enterprise Certificate Authority.
The security policy at ABC.com makes it necessary to examine revoked certificate information.
You need to make sure that the revoked certificate information is available at all times.
What should you do to achieve that?
A. Add and configure a new GPO (Group Policy Object) that enables users to accept peer
certificates and link the GPO to the domain.
B. Configure and use a GPO to publish a list of trusted certificate authorities to the domain
C. Configure and publish an OCSP (Online certificate status protocol) responder through ISAS
(Internet Security and Acceleration Server) array.
D. Use network load balancing and publish an OCSP responder.
E. None of the above
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/ee619754%28v=ws.10%29.aspx
QUESTION 29
As the Company administrator you had installed a read-only domain controller (RODC) server at remote location.
The remote location doesn’t provide enough physical security for the server.
What should you do to allow administrative accounts to replicate authentication information to Read-Only Domain Controllers?
A. Remove any administrative accounts from RODC’s group
B. Add administrative accounts to the domain
Allowed RODC Password Replication group
C. Set the Deny on Receive as permission for administrative accounts on the RODC computer
account Security tab for the Group Policy Object (GPO)
D. Configure a new Group Policy Object (GPO) with the Account Lockout settings enabled.
Link the GPO to the remote location.
Activate the Read Allow and the Apply group policy
Allow permissions for the administrators on the Security tab for the GPO.
E. None of the above
Answer: B
Explanation:
http://technet.microsoft.com/en-us/library/cc730883%28v=ws.10%29.aspx
QUESTION 30
ABC.com boasts a two-node Network Load Balancing cluster which is called web. L2P.com.
The purpose of this cluster is to provide load balancing and high availability of the intranet website only.
With monitoring the cluster, you discover that the users can view the Network Load Balancing cluster in their Network Neighborhood and they can use it to connect to various services by using the name web.L2P.com.
You also discover that there is only one port rule configured for Network Load Balancing cluster. You have to configure web.L2P.com NLB cluster to accept HTTP traffic only.
Which two actions should you perform to achieve this objective? (Choose two answers. Each answer is part of the complete solution)
A. Create a new rule for TCP port 80 by using the Network Load Balancing Cluster console
B. Run the wlbs disable command on the cluster nodes
C. Assign a unique port rule for NLB cluster by using the NLB Cluster console
D. Delete the default port rules through Network Load Balancing Cluster console
Answer: AD
Explanation:
http://technet.microsoft.com/en-us/library/cc733056.aspx
Create a new Network Load Balancing Port Rule
Port rules control how a Network Load Balancing (NLB) cluster functions.
To maximize control of various types of TCP/IP traffic, you can set up port rules to control how each port’s cluster-network traffic is handled. The method by which a port’s network traffic is handled is called its filtering mode. There are three possible filtering modes: Multiple hosts, Single host, and Disabled.
You can also specify that a filtering mode apply to a numerical range of ports. You do this by defining a port rule with a set of configuration parameters that define the filtering mode.
Each rule consists of the following configuration parameters:
The virtual IP address that the rule should apply to
The TCP or UDP port range that this rule should apply to
The protocols that this rule should apply to, including TCP, UDP, or both
The filtering mode that specifies how the cluster handles traffic, which is described by the port range and the protocols
In addition, you can select one of three options for client affinity: None, Single, or Network. Single and Network are used to ensure that all network traffic from a particular client is directed to the same cluster host.
To allow NLB to properly handle IP fragments, you should avoid using None when you select UDP or Both for your protocol setting. As an extension to the Single and Network options, you can configure a time-out setting to preserve client affinity when the configuration of an NLB cluster is changed. This extension also allows clients to keep affinity to a cluster host even if there are no active, existing connections from the client to the host.
2016 Valid Microsoft 70-640 Exam Preparation Materials:
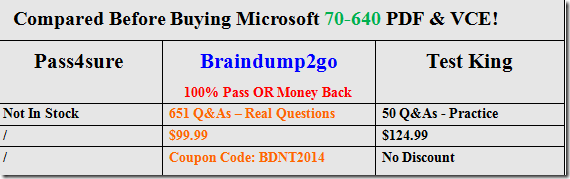
1.|Latest 70-640 PDF Dumps and 70-640 VCE Dumps 651Q&As Download in Braindump2go:http://www.braindump2go.com/70-640.html
2.|Newest 70-640 Exam Questions – Google Drive:https://drive.google.com/folderview?id=0B9YP8B9sF_gNX1czTkpVMlc4OTg&usp=sharing
3.|More 70-640 Practice Questions:https://drive.google.com/folderview?id=0B75b5xYLjSSNflhnZS1rbDE1cGd1c1g1UWZEdXUxSkwtbExFWU5YSGxBRGRTTTQ2M1ZBb2c&usp=sharing